Dark Reading is running a story regarding a 3 week malware campaign in which Online Ad Networks enabled miscreants to redirect clicks to sites hosting the Angler Exploit Kit. The full story can be found here.
Note that the Security Community in general considers this a "big security blunder". However, of special note, is the following quote:
"A fraudulent ad server using HTTPS. We were basically blind to it," he says.
Question - are you still putting off HTTPS Decryption? Wouldn't it be nice if you had Security Controls with visibility into your encrypted traffic and that ongoing attack??
Response - Yes, HTTPS Decryption and proxies in general can be complex... but ESPO Systems can help you with our Best Practices. :-) An additional advantage to consider, as identified within another story running on Dark Reading regarding questionable CAs, found here, is easily addressed when you have a Websense Proxy and thereby have a central location to control CAs:
Tuesday, September 15, 2015
Tuesday, September 1, 2015
Cisco = Security?
An attack is currently underway in which a dropper file downloads additional malware from the following site:
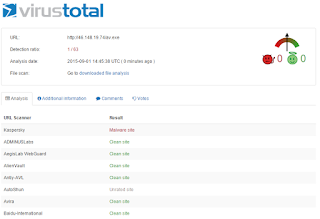
Per the VirusTotal screenshot below, only 1 of 63 vendors is blocking... other than Websense:
If you've bought into the Cisco dogma of a unified/secure network, you're likely hoping your IronPort Web Proxy with associated SenderBase Reputation System will protect you. Ummmmm... no:
Per the VirusTotal screenshot below, only 1 of 63 vendors is blocking... other than Websense:
If you've bought into the Cisco dogma of a unified/secure network, you're likely hoping your IronPort Web Proxy with associated SenderBase Reputation System will protect you. Ummmmm... no:
Tuesday, August 25, 2015
Another day...
...another attack in which the "Premium" Security Guys (McAfee & Symantec) are AWOL:
- Email traversing the internet this morning with a subject of "Invoice 26949 from I SPI Ltd". The M$ Word attachment is named Report For Inv_26949_from_I__SPI_Ltd_7888.doc
- Per this Websense File Sandbox Report, the malware modifies 23 Files, 2 Processes and 417 Registry Settings. However, the "Premium" Security/AV Guys currently find no problem with the file:
- Additionally, per the above Websense File Sandbox report, you'll notice that the malware also phones home to a site in Poland to download an additional exe. You may therefore ask, "can the "Premium" Security Guys at least protect me from this portion of the blended threat?" Ummm... no:
- Email traversing the internet this morning with a subject of "Invoice 26949 from I SPI Ltd". The M$ Word attachment is named Report For Inv_26949_from_I__SPI_Ltd_7888.doc
- Per this Websense File Sandbox Report, the malware modifies 23 Files, 2 Processes and 417 Registry Settings. However, the "Premium" Security/AV Guys currently find no problem with the file:
- Additionally, per the above Websense File Sandbox report, you'll notice that the malware also phones home to a site in Poland to download an additional exe. You may therefore ask, "can the "Premium" Security Guys at least protect me from this portion of the blended threat?" Ummm... no:
Friday, August 14, 2015
McAfee & Symantec... asleep at the wheel
Remind me again how we block malicious macros in Microsoft Files. Attachment blocking? Nope... not if it's a MS Office file. Antispam signatures? Kinda... but not 100% effective. Antivirus? Well... that's what we've put our trust in for the last decade. Good decision? Consider the following:
- Email traversing the internet this morning with a subject of "invoice" and an attached excel file:
- Per this Websense File Sandbox Report, the file modifies 53 Registry Settings and downloads an executable from a recently compromised site. In fact, the download is from a valid government site for the City of Noale Italy that has recently been compromised. Quick Question/Test - would your web filtering solution block that HTTP connection? :-)
- Lastly, and as is so often the case, the vendors who command such a premium for reactive signature-based AV solutions (McAfee and Symantec) are again MIA. Would it, therefore, make sense to reduce your AV budget by purchasing one of the vendors referenced below, and then reapply those savings towards an advanced security solution?
- Email traversing the internet this morning with a subject of "invoice" and an attached excel file:
- Per this Websense File Sandbox Report, the file modifies 53 Registry Settings and downloads an executable from a recently compromised site. In fact, the download is from a valid government site for the City of Noale Italy that has recently been compromised. Quick Question/Test - would your web filtering solution block that HTTP connection? :-)
- Lastly, and as is so often the case, the vendors who command such a premium for reactive signature-based AV solutions (McAfee and Symantec) are again MIA. Would it, therefore, make sense to reduce your AV budget by purchasing one of the vendors referenced below, and then reapply those savings towards an advanced security solution?
Thursday, August 6, 2015
Symantec Focused on Split?
As Symantec finally realizes that Security + Storage does not equal a valid business model and thereby prepares for their upcoming split, we at ESPO ask a question - is Symantec focused on Wall Street or your security? Consider the following:
- An ~80KB M$ Word doc with malicious macro is traversing the Internet today with a subject line of "Debit". The Websense File Sandbox report can be found here. Note how the malware performs a Zeus-like HTTP POST to a malware site in Germany.
- Convinced it's a bad file that you wouldn't want your Finance Dept receiving? Convinced that your Symantec AV has you covered?? May want to think again regarding that second question:
In closing, it's a nice to see McAfee catching this latest variant as we've beaten up on them recently. However, we still strongly advise clients put a File Sandboxing solution in place ASAP.
- An ~80KB M$ Word doc with malicious macro is traversing the Internet today with a subject line of "Debit". The Websense File Sandbox report can be found here. Note how the malware performs a Zeus-like HTTP POST to a malware site in Germany.
- Convinced it's a bad file that you wouldn't want your Finance Dept receiving? Convinced that your Symantec AV has you covered?? May want to think again regarding that second question:
In closing, it's a nice to see McAfee catching this latest variant as we've beaten up on them recently. However, we still strongly advise clients put a File Sandboxing solution in place ASAP.
Wednesday, July 22, 2015
Magic Quadrant for AV?
No disrespect to the team at Gartner, they are top notch people, but, is there really any value in creating a Magic Quadrant for AntiVirus? The folks at Intel/McAfee were certainly proud of their 7th consecutive year of placement in it, as seen here... even though we've demonstrated their poor catch rate many times in past blog posts. Another example from this morning:
- Emails are traversing the internet this morning with various email subjects that generally refer to international money transfers. Most importantly, a ~160k M$ Word doc is attached that leverages a malicious macro. Details regarding the registry modifications and associated phone home can be found in this Websense File Sandbox Report.
- Importantly, within the report, you will find a link to upload the file to VirusTotal in realtime. Hopefully we will see Symantec and McAfee update their signatures by end-of-business (West Coast Time of course ;-) and detect the file's malicious intent. However, as is all too often the case, you are left to rely upon your antispam sigs/reputation scores (which are 100% accurate right?) to stop these email msgs as the AV vendors are mostly blind to it now:
- Emails are traversing the internet this morning with various email subjects that generally refer to international money transfers. Most importantly, a ~160k M$ Word doc is attached that leverages a malicious macro. Details regarding the registry modifications and associated phone home can be found in this Websense File Sandbox Report.
- Importantly, within the report, you will find a link to upload the file to VirusTotal in realtime. Hopefully we will see Symantec and McAfee update their signatures by end-of-business (West Coast Time of course ;-) and detect the file's malicious intent. However, as is all too often the case, you are left to rely upon your antispam sigs/reputation scores (which are 100% accurate right?) to stop these email msgs as the AV vendors are mostly blind to it now:
Thursday, July 9, 2015
prodasynth.com compromised
This formerly clean site, dedicated to cosmetic sales in France, has been compromised and is now hosting malware:
Redirection to it is primarily driven by a blended threat lure propagating via email, and, unfortunately... only 1 of 63 Web Security Vendors (other than Raytheon|Websense) has detected the compromised site:
Lastly, what type of malware is being hosted you may ask? Well... it's a Dridex Dropper File attempting to steal your banking credentials/money (below). It's therefore slightly important ;-)
Redirection to it is primarily driven by a blended threat lure propagating via email, and, unfortunately... only 1 of 63 Web Security Vendors (other than Raytheon|Websense) has detected the compromised site:
Lastly, what type of malware is being hosted you may ask? Well... it's a Dridex Dropper File attempting to steal your banking credentials/money (below). It's therefore slightly important ;-)
Subscribe to:
Comments (Atom)