An Excel Spreadsheet w/malicious macro (serving as a dropper) is propagating across the Internet this morning. Raytheon|Websense File Sandbox Report found here.
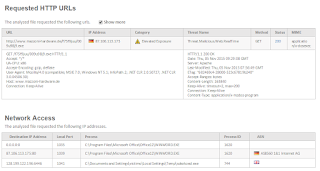
Per the above link, the dropper is pulling an additional executable from Japan (via HTTP) and phoning home on High Numbered TCP Ports to Mother Russia:
Unfortunately, this malware is considered clean by Symantec:
Time to rethink your Security Controls?
Tuesday, November 10, 2015
Thursday, November 5, 2015
O Brothers, Where Art Thou?
Word doc w/malicious macro (Websense File Sandbox Report found here) is on the loose this morning:
Per the above link, the downloader not only pulls another exe from a site in Germany... but also communicates out to a known botnet on a high number port (TCP:6446):
Finally, our Brothers-In-Arms (the AntiVirus guys), are AWOL... not a single engine detects this file currently:
In summary, check your firewall logs for the IPs referenced above. If you see them, remove the PC from the network... your user most likely downloaded the file via email or webmail. Lastly, call us to identify how you can secure those threat vectors better. :-)
Per the above link, the downloader not only pulls another exe from a site in Germany... but also communicates out to a known botnet on a high number port (TCP:6446):
Finally, our Brothers-In-Arms (the AntiVirus guys), are AWOL... not a single engine detects this file currently:
In summary, check your firewall logs for the IPs referenced above. If you see them, remove the PC from the network... your user most likely downloaded the file via email or webmail. Lastly, call us to identify how you can secure those threat vectors better. :-)
Wednesday, October 28, 2015
Anatomy of an "Ongoing" Attack
Emails traversing the internet this morning with malicious Word Attachments:
As usual, AntiVirus coverage is spotty as only 5 of 55 Companies currently have a signature available (McAfee and Symantec are MIA again):
Per this Raytheon|Websense File Sandbox Report, and as is typical with today's Blended Threats, this dropper file pulls another malicious file via HTTP from a site in Germany:
However, something interesting is going on with this 2nd bouncing ball, it phones home to a site in Russia. Of particular interest is the HTTP Post:
Question - are you monitoring outbound HTTP Posts to determine if Intellectual Property or PII is being exfiltrated? Better Question - if the Post was encrypted via HTTPS... would you be able to decrypt it and gain visibility into the data leak?
As usual, AntiVirus coverage is spotty as only 5 of 55 Companies currently have a signature available (McAfee and Symantec are MIA again):
Per this Raytheon|Websense File Sandbox Report, and as is typical with today's Blended Threats, this dropper file pulls another malicious file via HTTP from a site in Germany:
However, something interesting is going on with this 2nd bouncing ball, it phones home to a site in Russia. Of particular interest is the HTTP Post:
Question - are you monitoring outbound HTTP Posts to determine if Intellectual Property or PII is being exfiltrated? Better Question - if the Post was encrypted via HTTPS... would you be able to decrypt it and gain visibility into the data leak?
Wednesday, October 21, 2015
FBI Takes Down Dridex?
Well... that's what the Register reported earlier this month. However, emails are propagating the Internet this morning which smell a lot like Dridex:
Why do we at ESPO Systems believe this to be Dridex? As you see above, the social engineering still revolves around financial concepts and malicious macros are again being leveraged within M$ Office attachments... per this Websense File Sandbox Report.
What's the current AV Detection Rate you ask? Not good:
Why do we at ESPO Systems believe this to be Dridex? As you see above, the social engineering still revolves around financial concepts and malicious macros are again being leveraged within M$ Office attachments... per this Websense File Sandbox Report.
What's the current AV Detection Rate you ask? Not good:
Thursday, October 8, 2015
Pick your Poison
Interesting morning in that both M$ Word and Excel files are being distributed with malicious macros/downloaders that reach out for 983bv3.exe:
- Websense File Sandbox details for Word Downloader found here.
- Websense File Sandbox details for Excel Downloader found here.
As is the case all too frequently, if you're counting on your AV Vendor to protect you, your trust is misplaced:
What's the concern regarding this 983bv3.exe? How about the fact that it will modify 317 Registry Entries... details found here.
In summary, malware is too sophisticated to entrust the AV Vendors with our security. Call ESPO Systems to implement the next generation of Security Controls.
- Websense File Sandbox details for Word Downloader found here.
- Websense File Sandbox details for Excel Downloader found here.
As is the case all too frequently, if you're counting on your AV Vendor to protect you, your trust is misplaced:
What's the concern regarding this 983bv3.exe? How about the fact that it will modify 317 Registry Entries... details found here.
In summary, malware is too sophisticated to entrust the AV Vendors with our security. Call ESPO Systems to implement the next generation of Security Controls.
Thursday, October 1, 2015
Please Open... Not!
Email currently traversing the internet with an M$ Word attachment asking the recipient to "please open". Would your users respond properly?
Per this Websense File Sandbox report, the file is clearly malicious. Unfortunately, the "Premium AV Guys (McAfee & Symantec)" are asleep at the wheel again:
As such, you likely want to check your firewall logs to see if your users did indeed open the attachment/dropper and are therefore phoning home to the following IP Addresses:
Per this Websense File Sandbox report, the file is clearly malicious. Unfortunately, the "Premium AV Guys (McAfee & Symantec)" are asleep at the wheel again:
As such, you likely want to check your firewall logs to see if your users did indeed open the attachment/dropper and are therefore phoning home to the following IP Addresses:
Thursday, September 24, 2015
Blended Threats/Controls
Question - considering the plethora of Blended Threats which leverage both the Email & Web channels to exploit our networks... is it important that our Security Controls have visibility into both mediums?
Case in point - current phishing email traversing the internet which leverages legitimate looking graphics (directly below). Wouldn't it be nice if your web security solution knew of these spam/phishing URLs? On the flip side, wouldn't it be nice if your email security solution knew about malicious URLs?
As you'd expect, the link redirects to a malicious site... located in the Netherlands in this instance. Question - how important is it that your security solutions have a worldwide research team/presence?
Note that the site is attempting to obfuscate the content by leveraging javascript and Base64 encoding:
Final question - wouldn't it be nice if your security solutions not only had a worldwide presence in the Web & Email channels... but could also block active code (javascript, java, active-x) ala the Websense ACE Engine? :-)
Case in point - current phishing email traversing the internet which leverages legitimate looking graphics (directly below). Wouldn't it be nice if your web security solution knew of these spam/phishing URLs? On the flip side, wouldn't it be nice if your email security solution knew about malicious URLs?
As you'd expect, the link redirects to a malicious site... located in the Netherlands in this instance. Question - how important is it that your security solutions have a worldwide research team/presence?
Note that the site is attempting to obfuscate the content by leveraging javascript and Base64 encoding:
Final question - wouldn't it be nice if your security solutions not only had a worldwide presence in the Web & Email channels... but could also block active code (javascript, java, active-x) ala the Websense ACE Engine? :-)
Subscribe to:
Comments (Atom)