Around 7:30amCST an Excel Spreadsheet w/macro began propagating across the Internet. If you trust your security to the Anti Virus Vendors, you're likely sipping on a cup of coffee expecting to have an easy day heading into the weekend... as neither McAfee nor Symantec are currently detecting a problem:
However, per this Forcepoint File Sandbox Report, your day is about to change as this file is indeed malicious. Per the report, it attempts to modify 21 Files, 2 Processes and 412 Registry Entries. If that isn't bad enough, this Dropper File will also communicate to sites in Russia and Vietnam to pull down additional malware:
Additionally, if you've entrusted your Web Security to Cisco Ironport and are hoping the phone home to uggs-fashion.ru is blocked... you'll be disappointed. Per below, the site name implies it's a fashion site, and, the Senderbase Reputation System unfortunately agrees:
In summary, security is moving far too fast to rely upon AV Signatures. Contact ESPO Systems for a free consultation regarding how you can protect your IT Assets across the entire Kill Chain.
Friday, February 26, 2016
Thursday, February 18, 2016
Locky Ransomware on the Loose
It appears the Dridex Crew has expanded their Cyber Crime Portfolio from the stealing of login credentials to your favorite Financial Institution... to Ransomware. Case in point:
- M$ Word Documents with malicious macros are being distributed via email attachments (sound familiar).
First Question - Will your users allow you to block all inbound Microsoft Word attachments? Likely not...
Second Question - Are your spam prevention techniques 100% effective? Ummm... no.
Third Question - Should we therefore feel confident that your Anti Virus Solution has your back and will detect the file at the gateway or desktop? PLEASE!!!
- Thankfully, the Forcepoint File Sandboxing feature will detect this Ransomware. On the other hand, if you are using an inferior solution, you are likely seeing Help Desk Tickets describe something looking like this:
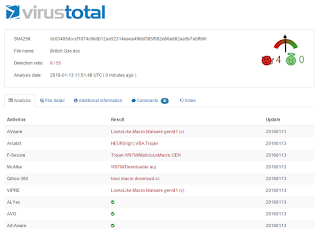
- Anyone care to know the current AV Detection Rate? Currently only 5 of 54 AV Engines are detecting the file properly. How long do you think it will take before McAfee and Symantec get their act together?
In summary, this is the same crew who took down the Hollywood Presbyterian Medical Center over the weekend. Do you wish to stay out of the news? Need help from an organization who performed over 600 Security Projects in 2015?? Contact ESPO Systems here.
- M$ Word Documents with malicious macros are being distributed via email attachments (sound familiar).
First Question - Will your users allow you to block all inbound Microsoft Word attachments? Likely not...
Second Question - Are your spam prevention techniques 100% effective? Ummm... no.
Third Question - Should we therefore feel confident that your Anti Virus Solution has your back and will detect the file at the gateway or desktop? PLEASE!!!
- Thankfully, the Forcepoint File Sandboxing feature will detect this Ransomware. On the other hand, if you are using an inferior solution, you are likely seeing Help Desk Tickets describe something looking like this:
- Anyone care to know the current AV Detection Rate? Currently only 5 of 54 AV Engines are detecting the file properly. How long do you think it will take before McAfee and Symantec get their act together?
In summary, this is the same crew who took down the Hollywood Presbyterian Medical Center over the weekend. Do you wish to stay out of the news? Need help from an organization who performed over 600 Security Projects in 2015?? Contact ESPO Systems here.
Wednesday, February 10, 2016
AS57389 ZNET-Mikronet Kft
OK... lets follow the bouncing ball again:
1. Microsoft Word doc is being propagated this morning that leverages a naming convention along the lines of "ReportforInvoicexxx.doc". We strongly recommend you block this file from being downloaded as it contains a malicious macro that modifies 24 Files, 2 Processes and 417 Registry Entries. Forcepoint File Sandbox Report here.
2. As is typically the case, the Anti-Virus Vendors are slow in responding as only 5 of 54 companies are accurately detecting the file as malware:
3. So... what does the malware do besides the aforementioned modifications? Per below, it makes an HTTP call outbound to download an additional file:
4. Whats happens when the 65fg67n file is downloaded? Per this Forcepoint File Sandbox Report, the malware author downloads updates from Microsoft (how nice of them to patch our boxes) and additionally phones home to the botnet via TCP Port 843 to a server in Hungary (AS # 57389). Hence the title of our post.
In summary, if you see outbound connections to 87.229.86.20 on your firewall... you have problems. Call ESPO Systems for a free consultation in regards to IT Controls across the entire Kill Chain.
1. Microsoft Word doc is being propagated this morning that leverages a naming convention along the lines of "ReportforInvoicexxx.doc". We strongly recommend you block this file from being downloaded as it contains a malicious macro that modifies 24 Files, 2 Processes and 417 Registry Entries. Forcepoint File Sandbox Report here.
2. As is typically the case, the Anti-Virus Vendors are slow in responding as only 5 of 54 companies are accurately detecting the file as malware:
3. So... what does the malware do besides the aforementioned modifications? Per below, it makes an HTTP call outbound to download an additional file:
4. Whats happens when the 65fg67n file is downloaded? Per this Forcepoint File Sandbox Report, the malware author downloads updates from Microsoft (how nice of them to patch our boxes) and additionally phones home to the botnet via TCP Port 843 to a server in Hungary (AS # 57389). Hence the title of our post.
In summary, if you see outbound connections to 87.229.86.20 on your firewall... you have problems. Call ESPO Systems for a free consultation in regards to IT Controls across the entire Kill Chain.
Tuesday, February 2, 2016
Symantec AWOL Again
Another day, another threat missed by the "Premium" AV/Security companies. Case in point:
- As of 7amCST a Microsoft Word Document w/Malicious Macro began propagating across the internet. Are we sure it's malicious? Yeah... pretty sure:
Forcepoint File Sandbox Report
- As seen above, the malware affects 2 Processes, 24 Files and 418 Registry Entries. If that isn't enough to convince you of it's malicious nature, how about the fact that it also phones home to a known Botnet, and, pulls down an additional executable via HTTP:
- Lastly, if you are hoping your Symantec Security Solution is going to protect you against this Dridex Attack (which is gunning for the login credentials to your bank)... your hope is misplaced as only 4 of 53 AV Companies are currently detecting this threat:
In summary, it's time to reduce your security spend on legacy security solutions (AV) and adopt Next Generation Solutions. Request a free ESPO Systems Consultation here.
- As of 7amCST a Microsoft Word Document w/Malicious Macro began propagating across the internet. Are we sure it's malicious? Yeah... pretty sure:
Forcepoint File Sandbox Report
- As seen above, the malware affects 2 Processes, 24 Files and 418 Registry Entries. If that isn't enough to convince you of it's malicious nature, how about the fact that it also phones home to a known Botnet, and, pulls down an additional executable via HTTP:
- Lastly, if you are hoping your Symantec Security Solution is going to protect you against this Dridex Attack (which is gunning for the login credentials to your bank)... your hope is misplaced as only 4 of 53 AV Companies are currently detecting this threat:
In summary, it's time to reduce your security spend on legacy security solutions (AV) and adopt Next Generation Solutions. Request a free ESPO Systems Consultation here.
Thursday, January 28, 2016
Trust Barracuda?
Yes... we agree that Barracuda is "cost effective". You too could create cost effective solutions if you leveraged open source tools. However, the question needs to be asked, are you willing to reduce your risk posture to save a few bucks? Case in point:
M$ Word file started propagating across the Internet with malicious macros at ~7:45amCST. This file is actually a Dropper File, as shown via this Forcepoint File Sandbox Report, which is attempting to infect your local files and phone home to a website in the US:
What is the Anti-Virus Coverage Rate you may ask for this Dropper File? Not good... only 5 companies currently detect it:
OK... lets assume your security controls have not blocked the download of the dropper, is your Barracuda Solution going to protect you from the download of the actual payload? Ummm... no:
In summary, please contact ESPO Systems if you'd like to implement controls to block the attack across the entire Kill Chain.
M$ Word file started propagating across the Internet with malicious macros at ~7:45amCST. This file is actually a Dropper File, as shown via this Forcepoint File Sandbox Report, which is attempting to infect your local files and phone home to a website in the US:
What is the Anti-Virus Coverage Rate you may ask for this Dropper File? Not good... only 5 companies currently detect it:
OK... lets assume your security controls have not blocked the download of the dropper, is your Barracuda Solution going to protect you from the download of the actual payload? Ummm... no:
In summary, please contact ESPO Systems if you'd like to implement controls to block the attack across the entire Kill Chain.
Wednesday, January 13, 2016
Symantec + Cisco = Bad Day
Do you have Symantec's AV + Cisco's Web Gateway? If so, you may be in for a bad day. Why? Malware is currently working it's way around the Internet that neither vendor is protecting against:
Per this Raytheon|Websense File Sandbox Report, a malicious Word Document is being propagated that is actually a Dropper File for Dridex. If you are hoping Symantec will protect your IT Assets against this threat... you will be disappointed:
Next, assuming the Dropper File was not detected, it's now downloading additional malware from a website on the GoDaddy domain:
If you are hoping your Cisco / IronPort Web Gateway is protecting your IT Assets... you will be disappointed again:
In summary, your security solution needs to be holistic... you need to have visibility into all 7 steps of the Kill Chain. Call ESPO Systems for a free consultation.
Per this Raytheon|Websense File Sandbox Report, a malicious Word Document is being propagated that is actually a Dropper File for Dridex. If you are hoping Symantec will protect your IT Assets against this threat... you will be disappointed:
Next, assuming the Dropper File was not detected, it's now downloading additional malware from a website on the GoDaddy domain:
If you are hoping your Cisco / IronPort Web Gateway is protecting your IT Assets... you will be disappointed again:
In summary, your security solution needs to be holistic... you need to have visibility into all 7 steps of the Kill Chain. Call ESPO Systems for a free consultation.
Tuesday, December 15, 2015
Cryptolocker being installed via HTTPS
We know, we know, we know... proxies are complex. It's much easier to install a Next Gen Firewall and check the box. However, what are you going to do about DLP? Additionally, what are you going to do about the latest Cryptolocker attack? Per here and below, Firefoxpatch.exe, which is indeed malware, is being distributed via the phaaccounty-taxes website:
Your answer may be to turn on HTTPS Decryption. We'll let you in on an ugly little secret... most Next Gen Firewalls have performance degradation issues when this feature is turned on per this NSS Labs Test:
Are we saying Next Gen Firewalls are not the answer? Not at all... they are absolutely part of the answer as the IPS, VPN, Application ID capabilities and traditional firewalling features are necessary. However, you need to augment these solutions with feature rich proxies ala the Raytheon|Websense APX Solution to enable a complete Security Architecture. Schedule a briefing with ESPO Systems today to learn more.
Your answer may be to turn on HTTPS Decryption. We'll let you in on an ugly little secret... most Next Gen Firewalls have performance degradation issues when this feature is turned on per this NSS Labs Test:
Are we saying Next Gen Firewalls are not the answer? Not at all... they are absolutely part of the answer as the IPS, VPN, Application ID capabilities and traditional firewalling features are necessary. However, you need to augment these solutions with feature rich proxies ala the Raytheon|Websense APX Solution to enable a complete Security Architecture. Schedule a briefing with ESPO Systems today to learn more.
Subscribe to:
Comments (Atom)