When McAfee acquired Secure Computing, we pretty much all suspected Dave DeWalt was putting lipstick on his pig in an attempt to create a liquidity event for himself. You could see a lack of integration and R&D investment from the start... much less an understanding of Network Security. Poor Intel is now stuck holding the goods. Case in point:
- Current MS Word Document making it's way around the Internet as of 1 hour ago and phoning home to Mother Russia per this Forcepoint Sandbox Report.
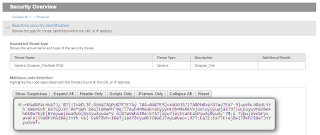
- As you'll note in the above report, the outbound call is detected in real-time by Forcepoint as a generic threat:
- What is the threat? The Forcepoint ACE Engine identifies it as a Dropper File:
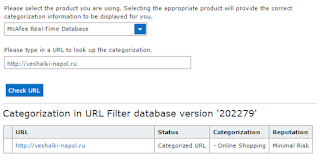
- What does Intel/McAfee think about the site? It's a Shopping site with Minimal Risk from their perspective:
Need help in ripping out your McAfee solution for a true single pane of glass? Connect w/ESPO Systems and request a free consultation.
Thursday, July 21, 2016
Thursday, July 7, 2016
Own Your Network Security?
Cisco has recently changed their Marketing to correspond with their change of leadership/CEO. Lets test out their current "own your network security" mantra:
1. Microsoft Word documents are propagating across the Internet with malicious macros. If your users have opened it, they would have seen this:
2. If your users enabled editing (the macro), unbeknownst to them, they would have initiated an outbound HTTP connection to this site in Germany:
3. Question - Would Cisco have enabled you to own your security... or been owned? Based on what we see below, it looks like you are owned:
In summary, our work can be double checked via this Forcepoint File Sandbox Report. If you agree with our conclusions, it's likely time to discuss how you can improve your Security Controls. Learn more about our Forcepoint Services here.
1. Microsoft Word documents are propagating across the Internet with malicious macros. If your users have opened it, they would have seen this:
2. If your users enabled editing (the macro), unbeknownst to them, they would have initiated an outbound HTTP connection to this site in Germany:
3. Question - Would Cisco have enabled you to own your security... or been owned? Based on what we see below, it looks like you are owned:
In summary, our work can be double checked via this Forcepoint File Sandbox Report. If you agree with our conclusions, it's likely time to discuss how you can improve your Security Controls. Learn more about our Forcepoint Services here.
Tuesday, June 14, 2016
To Russia with Love
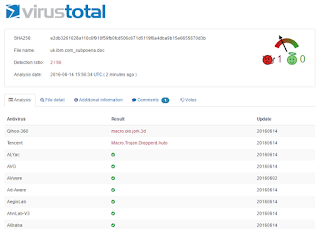
Yes... we know it was "From Russia with Love", however, in this case it's a Post not a Get. Say what? Well... there is a malicious M$ Word document/macro that is on the loose currently. As usual, the AV vendors are asleep at the wheel with only 2 of 57 solutions currently protecting our IT Assets:
Why are we so confident that McAfee and others are wrong? This Forcepoint Sandbox Report proves that rather conclusively.
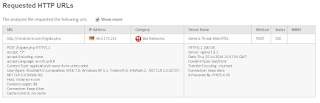
OK, Ok, ok... why "To Russia..."? Per below, the Dropper file performs an HTTP Post to a WWW site in Mother Russia. This is an obvious outlier as most HTTP/S traffic is Get based rather than Post.
Why would a Post occur rather than a Get? Likely to send out your confidential information. Question - do you have a Data Loss Prevention (DLP) solution monitoring those outbound Posts? What if it was HTTPS vs HTTP? Connect w/ESPO Systems for a free consultation.
Why are we so confident that McAfee and others are wrong? This Forcepoint Sandbox Report proves that rather conclusively.
OK, Ok, ok... why "To Russia..."? Per below, the Dropper file performs an HTTP Post to a WWW site in Mother Russia. This is an obvious outlier as most HTTP/S traffic is Get based rather than Post.
Why would a Post occur rather than a Get? Likely to send out your confidential information. Question - do you have a Data Loss Prevention (DLP) solution monitoring those outbound Posts? What if it was HTTPS vs HTTP? Connect w/ESPO Systems for a free consultation.
Tuesday, May 31, 2016
Macro Malware on the Loose
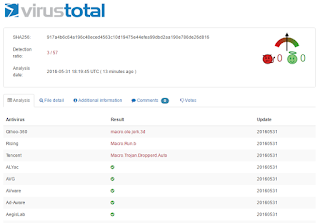
Heads Up! Another malicious MS Word file is on the loose with a very low detection rate. Forcepoint File Sandbox Report here.
Note that only 3 of 57 Anti Virus Companies are properly detecting this malware:
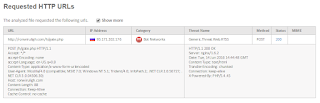
Importantly, per below, note that a number of outbound HTTP Gets occur in which additional malware is downloaded:
Are you safe with old fashion URL Filtering? Ummmm...nope. Per below, this Russian Site is new (Uncategorized). As such, you'll need a sophisticated anti-malware engine on your web proxy, ala Forcepoint's ACE Engine, to stop the 2nd stage of this attack:
Need more info about the Dridex Crew, who's targets have evolved from online banking credentials to this latest round of Locky Ransomware? See the ESPO Systems Multimedia Portal here.
Note that only 3 of 57 Anti Virus Companies are properly detecting this malware:
Importantly, per below, note that a number of outbound HTTP Gets occur in which additional malware is downloaded:
Are you safe with old fashion URL Filtering? Ummmm...nope. Per below, this Russian Site is new (Uncategorized). As such, you'll need a sophisticated anti-malware engine on your web proxy, ala Forcepoint's ACE Engine, to stop the 2nd stage of this attack:
Need more info about the Dridex Crew, who's targets have evolved from online banking credentials to this latest round of Locky Ransomware? See the ESPO Systems Multimedia Portal here.
Wednesday, April 20, 2016
Symantec Misses on Dropper
A malicious Microsoft Word File w/associated macro is making its way across the Internet this morning. How do we know? Our Forcepoint Sandbox detected it... report here.
Unfortunately, and as is the case all too often, Symantec is not detecting this malware as proven by VirusTotal:
What makes us so certain that this file is indeed malicious? Per below, it's pulling another file down via HTTP:
What does that prove you may ask? Per below, that file is detected as another Dropper by our Forcepoint ACE Engine which is resident on our proxies:
In summary, AntiVirus is a commodity. Do not buy into the pitch that it will solve your security problems. Reduce your security spend on AV and insert Next Gen Security Solutions. Call ESPO Systems for a free consultation/demonstration.
Unfortunately, and as is the case all too often, Symantec is not detecting this malware as proven by VirusTotal:
What makes us so certain that this file is indeed malicious? Per below, it's pulling another file down via HTTP:
What does that prove you may ask? Per below, that file is detected as another Dropper by our Forcepoint ACE Engine which is resident on our proxies:
In summary, AntiVirus is a commodity. Do not buy into the pitch that it will solve your security problems. Reduce your security spend on AV and insert Next Gen Security Solutions. Call ESPO Systems for a free consultation/demonstration.
Tuesday, March 29, 2016
Control-as-a-Service (CaaS)
Anyone tired of hearing that the following architectures solve all the world's problems - SaaS, IaaS, Cloud? Here's a novel concept, why don't we take "control" of our solutions, from a security perspective, and leave our fate in our own hands. Case in point - MedStar Health:
- Per this Computerworld Article, MedStar was attacked over the weekend with the same ransomware that hit the Hollywood Presbyterian Medical Center in mid-February. Per the report, the organization lost "control" of files and their system. Does that sound like a potential HIPAA issue to you?
- Per this earlier ESPO Systems Blog, the Locky Ransomware is leveraging holes in our security controls. To be precise, the malware authors know we dare not block Microsoft Attachments... even if they have malicious macros. They also know AV Signatures are too slow to provide value. As such, the only answer is Sandboxing... ala Forcepoint's Solution.
- So, you likely are asking, what does the MedStar Health Organization use to protect against these threats? Well... they've bought into the Cloud Saves Everything dogma and have given "control" of their security to Google/Postini:
One final question, considering MedStar has given up "control" of their email security, is there much of a chance that outbound email is being monitored for PII or PHI? It may be time to take back control of our security solutions.
- Per this Computerworld Article, MedStar was attacked over the weekend with the same ransomware that hit the Hollywood Presbyterian Medical Center in mid-February. Per the report, the organization lost "control" of files and their system. Does that sound like a potential HIPAA issue to you?
- Per this earlier ESPO Systems Blog, the Locky Ransomware is leveraging holes in our security controls. To be precise, the malware authors know we dare not block Microsoft Attachments... even if they have malicious macros. They also know AV Signatures are too slow to provide value. As such, the only answer is Sandboxing... ala Forcepoint's Solution.
- So, you likely are asking, what does the MedStar Health Organization use to protect against these threats? Well... they've bought into the Cloud Saves Everything dogma and have given "control" of their security to Google/Postini:
One final question, considering MedStar has given up "control" of their email security, is there much of a chance that outbound email is being monitored for PII or PHI? It may be time to take back control of our security solutions.
Thursday, March 3, 2016
Comprehensive Threat Protection?
With the RSA Security Conference coming to a close, we suspect a lot of Security Pros are asking the same questions as us regarding all the dollars thrown at marketing, "really"? That's not to say this intangible expense isn't needed. If the products perform as advertised... we need to get-the-word-out. However, when the marketing is nothing other than an attempt to obfuscate what is happening in the real word, as is the case currently with McAfee, it is our obligation to shed light on this. Case in point:
McAfee is proclaiming to the world that they provide "Comprehensive Threat Protection"
However, as is often the case, malware is currently propagating across the internet via Microsoft Word Documents with Malicious Macros in which McAfee is not providing the protection their Mkting Dept claims. Per below, only 3 of 55 AV Engines currently find a problem with this file:
Need further proof that the file is indeed malicious? Note that files are dropped locally, processes are affected and outbound HTTP calls to Mother Russia are occurring:
In summary, and as is often stated on this blog, AV is a commodity. Improve your security posture by implementing Next Gen Solutions with the cost savings found by reducing your spend on AV.
McAfee is proclaiming to the world that they provide "Comprehensive Threat Protection"
However, as is often the case, malware is currently propagating across the internet via Microsoft Word Documents with Malicious Macros in which McAfee is not providing the protection their Mkting Dept claims. Per below, only 3 of 55 AV Engines currently find a problem with this file:
Need further proof that the file is indeed malicious? Note that files are dropped locally, processes are affected and outbound HTTP calls to Mother Russia are occurring:
In summary, and as is often stated on this blog, AV is a commodity. Improve your security posture by implementing Next Gen Solutions with the cost savings found by reducing your spend on AV.
Subscribe to:
Comments (Atom)